Fortinet warns of actively abused zero-day leak in VPN software
Fortinet warns of actively abused zero-day leak in VPN software
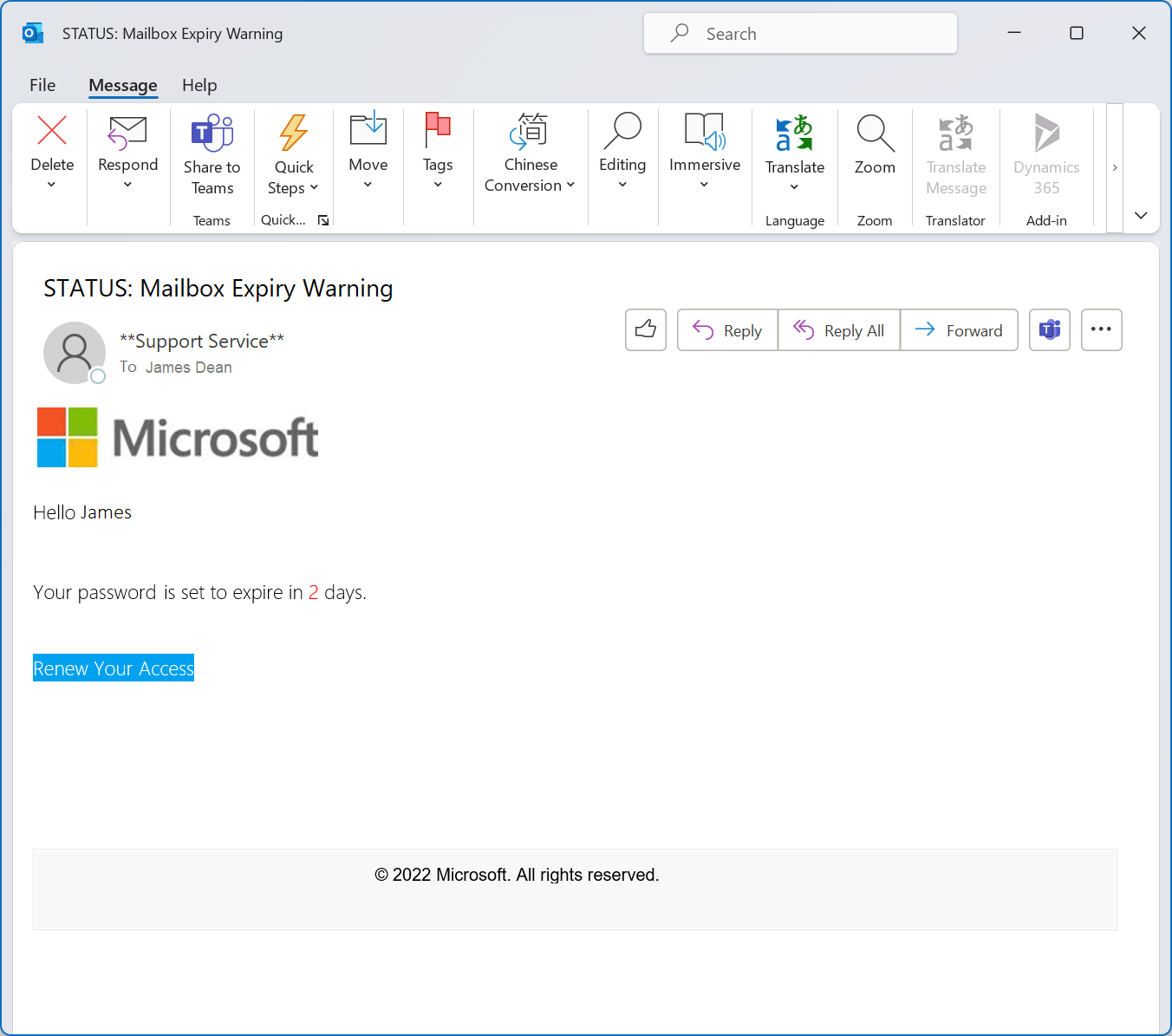
Fortinet is warning organizations of an actively exploited zero-day vulnerability in FortiOS SSL-VPN that could allow a remote attacker to take over vulnerable VPN servers. By sending specially crafted requests, an attacker can cause a heap-based buffer overflow and execute code on the system. Attackers do not need any credentials to carry out the attack.
The impact of the vulnerability has been assessed on a scale of 1 to 10 with a 9.3. Fortinet says the vulnerability, designated CVE-2022-42475 , was actively attacked even before the release of the security update, but does not provide further details about the target of the attacks. The security bulletin does contain information that can be used to recognize a successful attack on the VPN server.
“Vulnerabilities in VPN interfaces can therefore provide a starting point to penetrate a network, after which other systems may also be compromised. Depending on the situation, an attacker can, for example, gain access to sensitive information in this way or carry out a ransomware attack” , according to the National Cyber Security Center.
The Australian Cyber Security Center and the American Cybersecurity and Infrastructure Security Agency are calling on organizations to immediately install the security update and check whether their VPN servers have not been compromised.
Do you have a Fortinet Firewall installed in your organization? Reach out to us for assistance with the security update installation.
Contact us at: [email protected]